Threats: Page 2
-
North Korea-linked actor targets Web3 execs in social-engineering campaign
Founders and other top executives were compromised to gain access to crypto wallets.
By David Jones • April 27, 2026 -
US, UK authorities warn that Firestarter backdoor malware survives patching
A federal agency was impacted by a hacking campaign that exploited flaws in Cisco devices.
By David Jones • April 27, 2026 -
 Explore the Trendline➔
Explore the Trendline➔
 Getty Images
Getty Images Trendline
TrendlineManaging identity sprawl
Cyber threat actors know the simplest way to hack into an enterprise and remain under the radar is with stolen, legitimate user credentials -- and cloud services and AI are making managing and securing digital identities more challenging than ever.
By Cybersecurity Dive staff -
China disguises cyberattacks with ‘covert network’ botnets, US and allies warn
A new security advisory highlights Beijing’s stealthy techniques.
By Eric Geller • Updated April 23, 2026 -
Deep Dive
Iran-nexus threat groups refine attacks against critical infrastructure
State-sponsored and hacktivist groups have shown greater determination to damage or disable energy, water and other key sectors.
By David Jones • April 23, 2026 -
Phishing — sometimes with AI’s help — topped initial-access methods in Q1, Cisco says
Hackers can now spin up fake login pages without writing a single line of code.
By Eric Geller • April 22, 2026 -
CISA confirms exploitation of 3 more Cisco networking device vulnerabilities
Cisco revealed six critical flaws in widely used products in February. The government has now seen evidence that hackers are abusing four of them.
By Eric Geller • April 21, 2026 -
Vulnerability exploitation surges often precede disclosure, offering possible early warnings
Organizations can get ahead of major flaws with the right threat intelligence, according to a new report.
By Eric Geller • April 20, 2026 -
US joins nearly two dozen other countries in striking back against DDoS-for-hire platforms
Authorities around the world seized more than 50 websites associated with DDoS “booter” services.
By Eric Geller • April 17, 2026 -
CIOs fret over rising security concerns amid AI adoption
AI is emerging as a critical tool and a growing threat as CIOs struggle to balance innovation with risk, according to a new report.
By Scarlett Evans • April 16, 2026 -
FCC exempts Netgear from foreign router ban
The commission did not explain its action beyond citing a Defense Department determination.
By Eric Geller • April 15, 2026 -
Brute-force cyberattacks originating in Middle East surge in Q1
Hackers have primarily targeted SonicWall and Fortinet devices, according to researchers.
By David Jones • April 14, 2026 -
FCC signals continued commitment to Cyber Trust Mark program
The government approved a new lead overseer for its IoT device security labeling initiative.
By Eric Geller • Updated April 14, 2026 -
US, Indonesia shut down ‘sophisticated’ phishing kit
For a nominal fee, cybercriminals could rent access to a service that maliciously duplicated popular websites’ login portals.
By Eric Geller • April 13, 2026 -
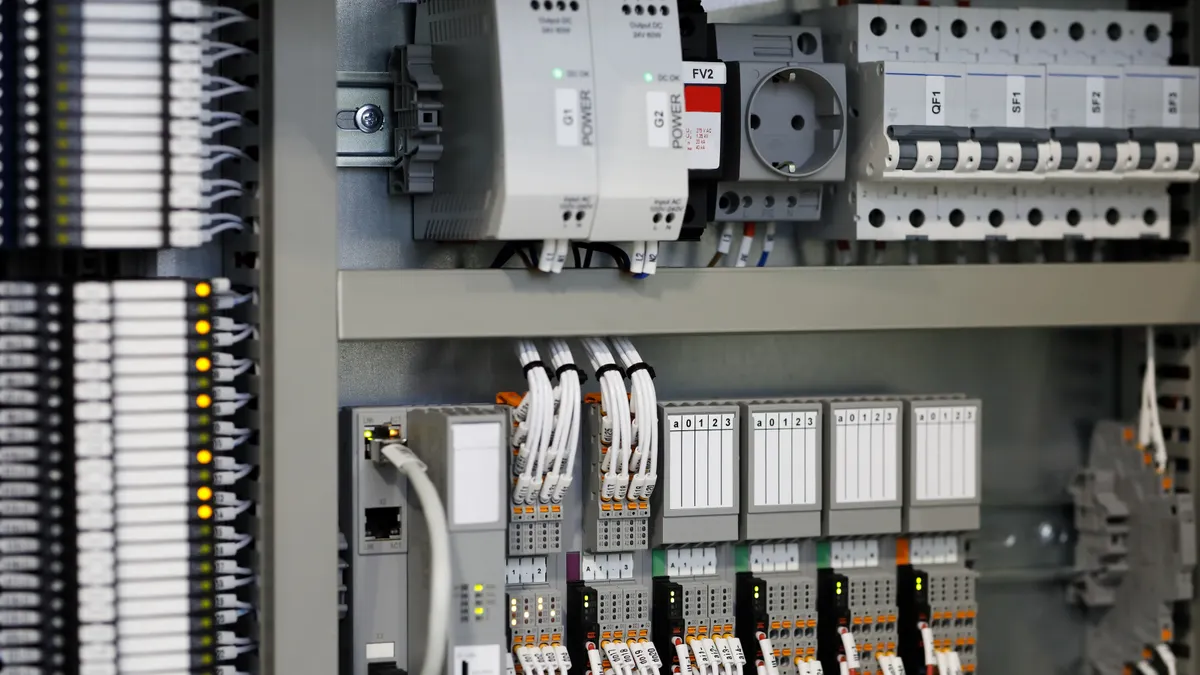
Nearly 4K industrial control devices vulnerable to Iran-linked hacking campaign
A research firm tallied the internet-exposed devices Iran is targeting and recommended mitigations for any infrastructure operator using them.
By Eric Geller • April 10, 2026 -
NERC is ‘actively monitoring the grid’ following Iran-linked cyber threat
Hackers have disrupted critical U.S. infrastructure by targeting programmable logic controllers, the Cybersecurity and Infrastructure Security Agency warned.
By Robert Walton • April 9, 2026 -
US operation evicts Russia from hacked SOHO routers used to breach critical infrastructure
The newly disclosed cyberattack campaign is the latest evidence of the threat end-of-life routers pose to major organizations.
By Eric Geller • Updated April 9, 2026 -
Iran-linked hackers target water, energy in US, FBI and CISA warn
Nation-state actors have exploited flaws in industrial programmable logic controllers, leading to disruption and financial losses.
By David Jones • April 8, 2026 -
Olympic Games, FIFA World Cup offer huge platforms, rich cyberattack surface
Global sporting events have become a lucrative target for criminal actors and geopolitical statements.
By David Jones • April 7, 2026 -
Threat cluster launches extortion campaign using social engineering
Researchers said the hackers are compromising business process outsourcers and targeting help desk support.
By David Jones • April 7, 2026 -
Government agencies see cyber threats as major barrier to tech improvements
Federal leaders also see opportunities to accelerate cyber defense with AI, according to a new report, but most agencies are still only testing AI tools.
By Eric Geller • April 3, 2026 -
Axios open-source library targeted in sophisticated supply chain attack
Researchers link the compromise to a North Korean adversary and warn the impacts could be wide ranging.
By David Jones • April 1, 2026 -
Iran-linked actors target Middle Eastern city governments to undermine missile-strike responses
The password-spraying campaign is the latest evidence that Iran is hitting back in cyberspace.
By Eric Geller • April 1, 2026 -
Iran actors’ claims raise questions about larger cyber threat to US, allies
Questions are being raised about the veracity and tactics of Iran-linked actors, amid claims that a large trove of Lockheed Martin data is on the market.
By David Jones • Updated March 31, 2026 -
Newly observed malware campaign likely combines AI and ClickFix
Using the techniques in tandem helps hackers evade detection, a security firm said.
By Eric Geller • March 30, 2026 -
Sponsored by Zurich Resilience Solutions
Why user behavior is the primary entry point for cyberattacks
Human error still drives 60% of breaches — here’s why attackers keep targeting users.
March 30, 2026