Cyberattacks
-
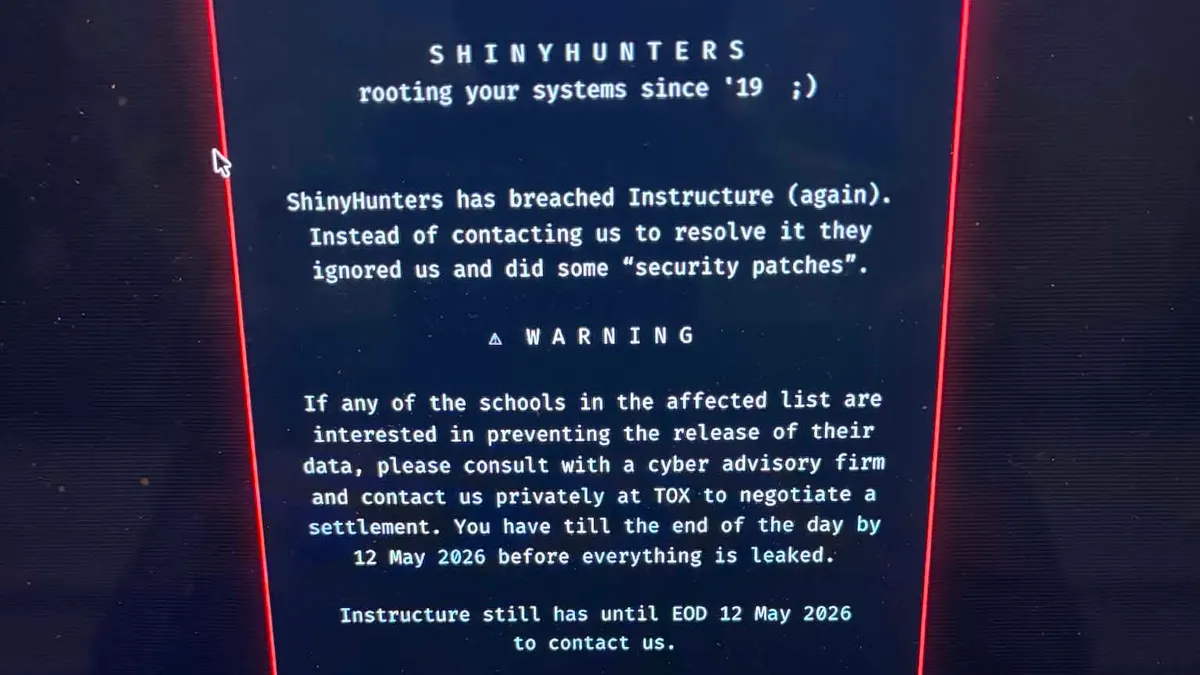
Second Canvas data breach causes major disruptions for schools, colleges
The Instructure-owned learning management system went offline on May 7 after a threat actor once again gained unauthorized access.
By Anna Merod • May 11, 2026 -
Sponsored by SHI
Identity is the new perimeter as rapid NHI proliferation threatens visibility and control
NHIs are linked to diverse assets across the enterprise technology ecosystem, creating a highly fragmented architecture and making it challenging for security teams to maintain visibility and control.
May 11, 2026 -
 Explore the Trendline➔
Explore the Trendline➔
 Getty Images
Getty Images
-
Instructure confirms cybersecurity incident
The ed tech company that operates Canvas said information impacted by the data breach includes messages, names, email addresses and student ID numbers.
By Anna Merod • May 8, 2026 -
Anthropic’s Claude used in attempted compromise of Mexican water utility
Researchers warn the incident highlights how AI tools can help untrained threat actors develop complex cyberattack capabilities.
By David Jones • May 8, 2026 -
Businesses hide vast majority of ransomware attacks, report finds
The security firm BlackFog said the number of disclosed incidents it tracked in Q1 was roughly one-tenth of the number of undisclosed incidents.
By Eric Geller • May 7, 2026 -
Sponsored by 1Password
How OpenClaw’s agent skills become an attack surface
OpenClaw and similar AI agent ecosystems, present pressing security risks.
May 4, 2026 -
As email phishing evolves, malicious attachments decline and QR codes surge
A new Microsoft report also describes the collapse of a once-dominant tool for generating phishing websites with fake CAPTCHAs.
By Eric Geller • May 1, 2026 -
CISA adds Microsoft, ConnectWise vulnerabilities to active exploitation catalog
Russia has used one of the flaws, security experts said, while North Korea has used the other.
By Eric Geller • April 29, 2026 -
‘Fundamental tension’ undermines manufacturers’ cybersecurity
A simple security mistake caused roughly one-quarter of all financial losses in the sector in 2025, cybersecurity insurer Resilience said.
By Eric Geller • April 28, 2026 -
North Korea-linked actor targets Web3 execs in social-engineering campaign
Founders and other top executives were compromised to gain access to crypto wallets.
By David Jones • April 27, 2026 -
Major critical infrastructure supplier reports cyberattack
Itron, which makes devices that measure energy and water use, said its operations were continuing, despite the intrusion.
By Eric Geller • April 27, 2026 -
US, UK authorities warn that Firestarter backdoor malware survives patching
A federal agency was impacted by a hacking campaign that exploited flaws in Cisco devices.
By David Jones • April 27, 2026 -
China disguises cyberattacks with ‘covert network’ botnets, US and allies warn
A new security advisory highlights Beijing’s stealthy techniques.
By Eric Geller • Updated April 23, 2026 -
Deep Dive
Iran-nexus threat groups refine attacks against critical infrastructure
State-sponsored and hacktivist groups have shown greater determination to damage or disable energy, water and other key sectors.
By David Jones • April 23, 2026 -
Phishing — sometimes with AI’s help — topped initial-access methods in Q1, Cisco says
Hackers can now spin up fake login pages without writing a single line of code.
By Eric Geller • April 22, 2026 -
CISA urges security teams to view environments following axios compromise
A suspected North Korea-linked actor is behind a supply chain attack on the widely used library.
By David Jones • April 21, 2026 -
Sponsored by Zurich Resilience Solutions
Beyond IT: Cybersecurity is a strategic business risk
Why cybersecurity now demands C-suite attention and accountability.
April 20, 2026 -
US joins nearly two dozen other countries in striking back against DDoS-for-hire platforms
Authorities around the world seized more than 50 websites associated with DDoS “booter” services.
By Eric Geller • April 17, 2026 -
FCC exempts Netgear from foreign router ban
The commission did not explain its action beyond citing a Defense Department determination.
By Eric Geller • April 15, 2026 -
Stryker warns of earnings fallout from March cyberattack
The medtech company was targeted in a wiper attack linked to an Iran-sponsored threat group.
By David Jones • April 10, 2026 -
Nearly 4K industrial control devices vulnerable to Iran-linked hacking campaign
A research firm tallied the internet-exposed devices Iran is targeting and recommended mitigations for any infrastructure operator using them.
By Eric Geller • April 10, 2026 -
NERC is ‘actively monitoring the grid’ following Iran-linked cyber threat
Hackers have disrupted critical U.S. infrastructure by targeting programmable logic controllers, the Cybersecurity and Infrastructure Security Agency warned.
By Robert Walton • April 9, 2026 -
US operation evicts Russia from hacked SOHO routers used to breach critical infrastructure
The newly disclosed cyberattack campaign is the latest evidence of the threat end-of-life routers pose to major organizations.
By Eric Geller • Updated April 9, 2026 -
Iran-linked hackers target water, energy in US, FBI and CISA warn
Nation-state actors have exploited flaws in industrial programmable logic controllers, leading to disruption and financial losses.
By David Jones • April 8, 2026 -
React2Shell vulnerability helps hackers steal credentials, AI platform keys and other sensitive data
The stolen information could help intruders plan follow-up attacks and breach more organizations, Cisco researchers said.
By Eric Geller • April 7, 2026