Opinion
The latest opinion pieces by industry thought leaders
If you are interested in having your voice heard on Cybersecurity Dive's Opinion page, please read our editorial guidelines and fill out the submission form here.
-
Gartner: How to prepare for and respond to today’s evolving threat landscape
With the emergence of AI, security operations teams must navigate a fast-moving generation of cyber threats.
Jeremy D'Hoinne, Distinguished Research VP, Gartner • Oct. 21, 2025 -
Gartner: How to create a compelling SOC narrative for executives
Focus on financial impact, efficiency and risk management to ensure informed cybersecurity investment decisions.
Pete Shoard, VP analyst, Gartner Cybersecurity Threat Detection & Response • June 9, 2025 -
How hospitality companies can stay ahead of cyberattacks this summer
Hotels are a popular target for cyberattacks, but industry collaboration and intelligence sharing can serve as defense mechanisms.
Pam Lindemoen • May 20, 2025 -
Gartner: How to build a secure enterprise cloud environment
There are plenty of frameworks, tools and strategies to help map out a risk-resilient cloud infrastructure.
Richard Bartley, Research VP, Gartner • April 21, 2025 -
Protecting the cloud: combating credential abuse and misconfigurations
To defend against two of today’s biggest cloud security threats, organizations must adapt and develop proactive strategies, Google Cloud’s Brian Roddy writes.
Brian Roddy • Dec. 5, 2024 -
Security awareness and training is a method, not an outcome
In 2024, the idea of human risk management shifted from concept to reality as frustrated CISOs looked for solutions beyond security awareness and training to make real change.
Jinan Budge • Nov. 20, 2024 -
Who should be in the room when purchasing cyber insurance?
Cyber exposure should be treated just as seriously as a fire event, each with a high potential to disrupt business for extended periods of time, Peter Hedberg of Corvus Insurance writes.
Peter Hedberg • Nov. 11, 2024 -
How to implement attack surface management
ASM is a core component of exposure management that organizations can leverage to enhance vulnerability management.
Steve Santos • Oct. 23, 2024 -
3 tips to building a robust AI security strategy
Organizations can reap bigger benefits from AI with guardrails that combine human oversight, strong underlying security architecture and technical controls.
Anton Chuvakin • Aug. 21, 2024 -
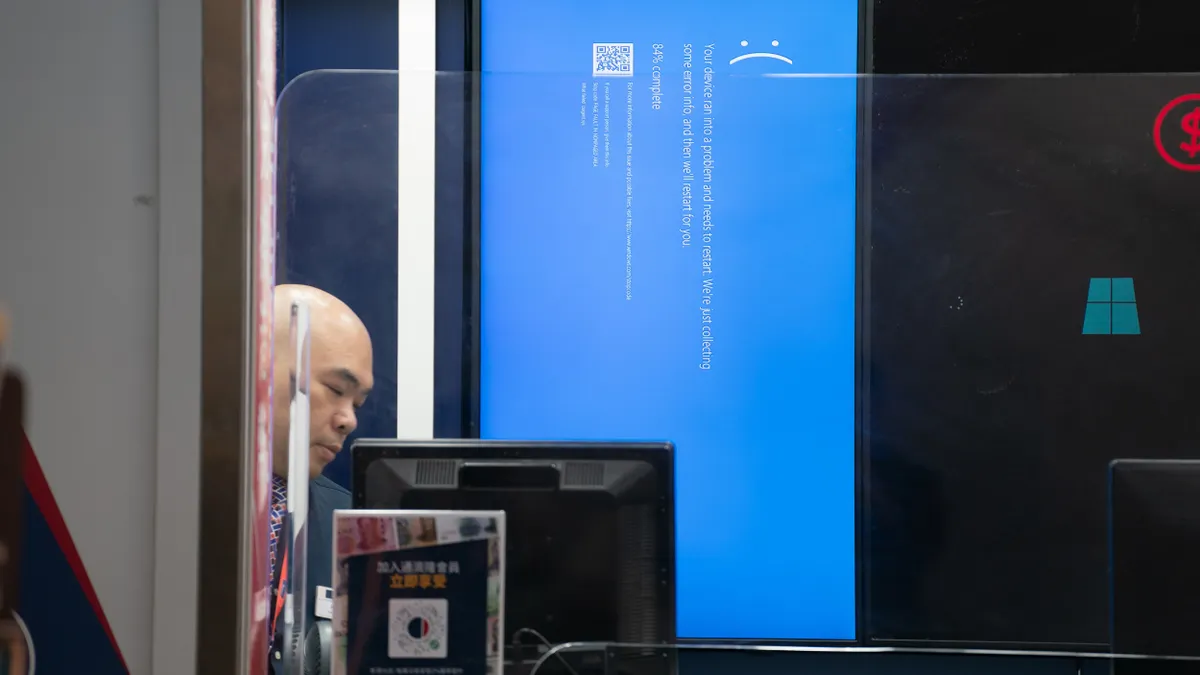
Misguided lessons from CrowdStrike outage could be disastrous
Some leaders think moving slowly is safer in light of global outages, but this approach is wrong when addressing cyber vulnerabilities and will lead to bigger problems.
Deepak Kumar • Aug. 13, 2024 -
How to identify and implement security automation use cases
It might be a “fun” engineering challenge to see what is possible to automate, but often the results will not justify the expense and effort, Gartner’s Kevin Schmidt writes.
Kevin Schmidt • June 4, 2024 -
The art of threat modeling: 3 frameworks to know
Organizations should use the frameworks in a manual or automated way to better understand the security threats they’re up against, Gartner’s William Dupre writes.
William Dupre • Updated April 24, 2024 -
Threat environment is changing for individuals and SMBs, White House order shows
An executive order is trying to prevent the large-scale transfer of Americans’ data, as countries seek troves of U.S. data for blackmail, AI training and analysis, among a multitude of other purposes.
Michael Kosak • March 18, 2024 -
Why trust is the most critical deliverable for CISOs
Instead of a list of nebulous targets, CISOs should focus on delivering trust to three key constituencies: their leadership, their peers and their inner circle.
Nader Henein • Nov. 6, 2023 -
Government investigation puts spotlight on password insecurity
A team working for the Department of Interior’s inspector general successfully cracked 1 in 5 active user passwords, a ratio that highlights traps in cybersecurity standards, Mike Kosask from LastPass writes.
Michael Kosak • Aug. 24, 2023 -
How to communicate data risk to the business
Data risk communications must be objective, pragmatic and clearly focused on the best interests of the organization to be effective, Gartner’s Joerg Fritsch writes.
Joerg Fritsch • July 31, 2023 -
Is cybersecurity doing enough to prevent the next Colonial Pipeline attack?
Two years have passed since the Colonial Pipeline incident, but critical infrastructure providers aren’t doing enough to proactively mitigate attacks.
Matthew Parsons, Brian Knudtson and Alex Reid • May 8, 2023 -
ChatGPT at work: What’s the cyber risk for employers?
The use of ChatGPT could run afoul of company policy, copyright concerns, customer confidentiality or even international privacy laws, BlackBerry’s CISO writes. Here’s what businesses should consider.
Arvind Raman • April 11, 2023 -
How cybersecurity leaders can tackle the skills shortage
Organizations that do not address talent shortages and diversity gaps could harm their current and future security programs, leading to suboptimal security and risk outcomes.
Akif Khan • April 5, 2023 -
The proposed SEC cyber incident disclosure rule is a positive change. But it won’t make organizations safer.
If organizations want to actually get serious about protecting themselves, they need to have a robust system for handling incidents when they happen.
Frank Shultz • March 27, 2023 -
Zero trust is moving from hype to reality
Organizations must plan ahead and invest in people and resources to succeed with zero trust, writes Gartner analyst John Watts.
John Watts • Feb. 10, 2023 -
Battle of the breach: Prioritizing proactive ransomware defense
Industry will soon face a reality where organizations are attacked every two seconds by threat actors that continue to evolve. So now what?
Sebastian Goodwin • Jan. 25, 2023 -
Why CISOs should prioritize DEI initiatives in 2023
Different mindsets can bring new and better solutions to the table that can mitigate advanced cyberthreats, Google Cloud’s director of the office of the CISO writes.
MK Palmore • Jan. 13, 2023 -
How to upgrade cybersecurity awareness training
Phishing attacks are not always as obvious as a direct message from someone pretending to be Elon Musk asking you to buy cryptocurrency. To better equip employees, cyber training needs an upgrade.
James Karimi • Dec. 12, 2022 -
How to implement an effective system to address third-party risk
Current processes for assessing and managing third-party cybersecurity risks are cumbersome and ineffective. CISOs must adopt new principles to address business exposure.
Sam Olyaei • Nov. 7, 2022