Threats
-
CISA urges security teams to check for software development compromises
The agency warned about a wave of attacks targeting credentials and other secrets across critical supply chains.
By David Jones • May 29, 2026 -
IBM’s new $5B initiative will help enterprises rapidly patch open-source vulnerabilities
The tech giant’s project could make it easier for businesses to safely use open-source packages.
By Eric Geller • May 28, 2026 -
 Explore the Trendline➔
Explore the Trendline➔
 Getty Images
Getty Images Trendline
TrendlineManaging identity sprawl
Cyber threat actors know the simplest way to hack into an enterprise and remain under the radar is with stolen, legitimate user credentials -- and cloud services and AI are making managing and securing digital identities more challenging than ever.
By Cybersecurity Dive staff -
Enterprise data is creeping its way into shadow AI tools
Executives and employees are clashing over usage policies as AI security concerns rise, an Okta report found.
By Paige Gross • May 28, 2026 -
Coordinated operation takes down Glassworm botnet
The botnet began in early 2025, targeting software developers across the open-source supply chain.
By David Jones • May 27, 2026 -
FBI warns about PhaaS platform used to access Microsoft 365 environments
Device code phishing enabled hackers to bypass multifactor authentication without credentials.
By David Jones • May 26, 2026 -
Iran-linked hackers target key US, allied sectors with sophisticated spear-phishing messages
Companies, particularly those in the affected industries, should harden their defenses against impersonation schemes, Palo Alto Networks said.
By Eric Geller • May 22, 2026 -
New York regulator calls for additional cyber mitigation amid heightened threat environment
The guidance from the state Department of Financial Services arises from concerns about frontier AI and threats linked to the Iran war and other geopolitical risks.
By David Jones • May 22, 2026 -
Grafana Labs links GitHub environment breach to TanStack npm supply chain attack
The company behind the widely used observability platform refused an extortion demand and has since taken steps to harden its security.
By David Jones • May 21, 2026 -
Microsoft disrupts cybercrime operation that hid behind legitimate software
The Fox Tempest malware-signing-as-a-service operation was linked to numerous ransomware attacks.
By David Jones • May 20, 2026 -
Compromised coding tool helped hackers breach thousands of GitHub repositories
The attack is the latest example of hackers’ intense focus on open-source packages.
By Eric Geller • May 20, 2026 -
Telecom sector launches its own private ISAC
Federal government involvement in an existing group chilled some cybersecurity discussions among major telecom providers. The new group is intended to alleviate those anxieties.
By Eric Geller • May 19, 2026 -
Grafana Labs says hacker gained access to codebase through leaked token
The company, which operates a widely used observability platform, is refusing to pay an extortion demand.
By David Jones • Updated May 19, 2026 -
Attackers exploit critical flaw in Cisco Catalyst SD-WAN Controller
Researchers discovered the authentication bypass vulnerability while investigating a prior issue in the same service.
By David Jones • May 15, 2026 -
MSPs need AI to fight AI-fueled cyberthreats: Guardz
Entry points haven’t changed, but the speed and scale of attacks have intensified, the security vendor found.
By Kelly Teal, Channel Dive contributor • May 15, 2026 -
Foxconn confirms cyberattack affecting some North American facilities
A ransomware group has claimed a major attack against the electronics manufacturer.
By David Jones • May 13, 2026 -
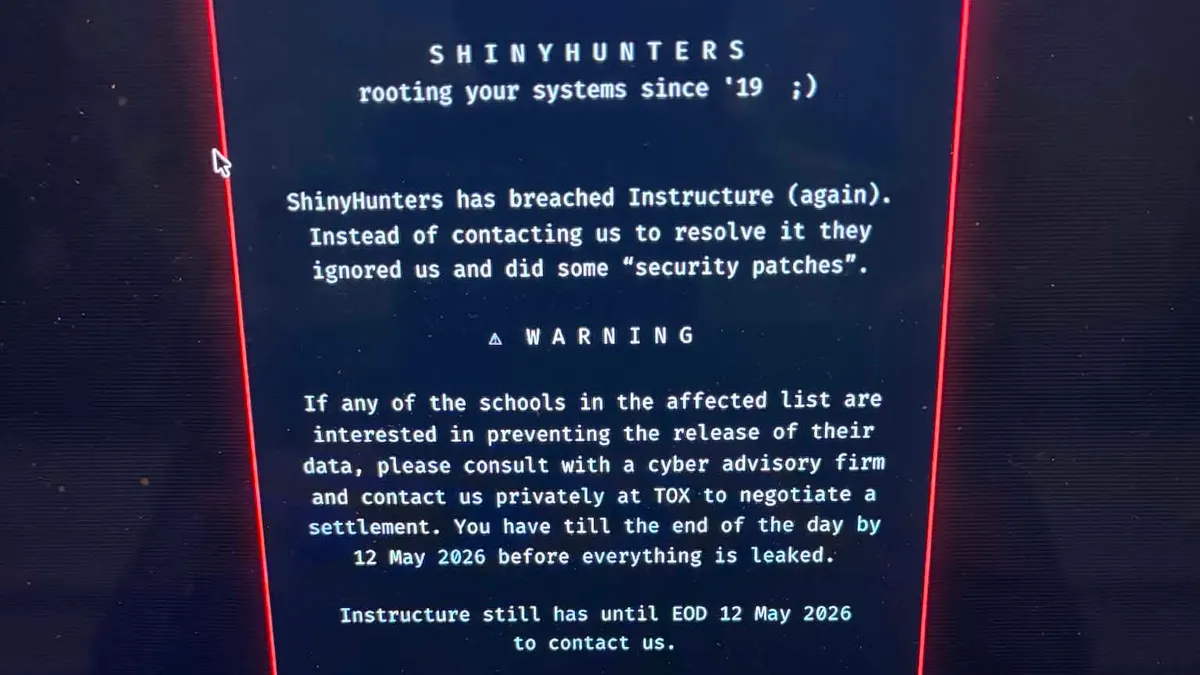
Canvas owner reaches ‘agreement’ with threat actors after data breach
Cybersecurity experts suggest that Instructure appears to have made a ransomware payment, which the FBI highly discourages.
By Anna Merod • May 13, 2026 -
AI and an absent government: Takeaways from RSAC 2026
Cybersecurity professionals discussed the balance between autonomy and oversight at the recent conference.
By Eric Geller • May 12, 2026 -
Second Canvas data breach causes major disruptions for schools, colleges
The Instructure-owned learning management system went offline on May 7 after a threat actor once again gained unauthorized access.
By Anna Merod • May 11, 2026 -
AI used to develop working zero-day exploit, researchers warn
A report by GTIG shows threat groups are increasingly leveraging AI to scale attacks. The exploitation attempt was disclosed and patched, preventing a mass incident.
By David Jones • May 11, 2026 -
Instructure confirms cybersecurity incident
The ed tech company that operates Canvas said information impacted by the data breach includes messages, names, email addresses and student ID numbers.
By Anna Merod • May 8, 2026 -
Palo Alto Networks warns state-linked cluster behind zero-day exploitation
A patch for the flaw, which hackers began targeting in early April, won’t be ready for another week.
By David Jones • May 7, 2026 -

 Retrieved from NASA's Moderate Resolution Imaging Spectroradiometer.
Retrieved from NASA's Moderate Resolution Imaging Spectroradiometer.
Iran-sponsored threat group behind false flag social engineering campaign
The state-linked actor has been masquerading as a criminal ransomware group in attacks targeting U.S. organizations.
By David Jones • May 6, 2026 -

 R. Eskalis/NIST. Retrieved from NIST.
R. Eskalis/NIST. Retrieved from NIST.
NIST will test three major tech firms’ frontier AI models for cybersecurity risks
After Anthropic’s announcement of Claude Mythos, agencies across the government are racing to get ahead of new AI models’ potential dangers.
By Eric Geller • Updated May 21, 2026 -
CISA urges critical infrastructure firms to ‘fortify’ before it’s too late
As concerns mount about potential cyber sabotage by the Chinese government, the U.S. is warning operators to practice maintaining services in a degraded state.
By Eric Geller • Updated May 5, 2026 -
White House questions tech industry on defensive AI use, cybersecurity resilience
Companies may be reluctant to answer some of the government’s questions, given the sensitive topics they address.
By Eric Geller • May 1, 2026