Strategy
-
New York regulator calls for additional cyber mitigation amid heightened threat environment
The guidance from the state Department of Financial Services arises from concerns about frontier AI and threats linked to the Iran war and other geopolitical risks.
By David Jones • May 22, 2026 -
CISA asks cybersecurity community to alert it to vulnerability exploitation
The agency wants to ensure that its public catalog of actively exploited flaws is as comprehensive as possible.
By Eric Geller • May 21, 2026 -
 Explore the Trendline➔
Explore the Trendline➔
 IPGGutenbergUKLtd via Getty Images
IPGGutenbergUKLtd via Getty Images Trendline
TrendlineThe Cybersecurity Skills Gap
From AI to federal budget cuts, the nature of cybersecurity work is changing faster than ever.
By Cybersecurity Dive staff -
Microsoft disrupts cybercrime operation that hid behind legitimate software
The Fox Tempest malware-signing-as-a-service operation was linked to numerous ransomware attacks.
By David Jones • May 20, 2026 -
Telecom sector launches its own private ISAC
Federal government involvement in an existing group chilled some cybersecurity discussions among major telecom providers. The new group is intended to alleviate those anxieties.
By Eric Geller • May 19, 2026 -
Deep Dive
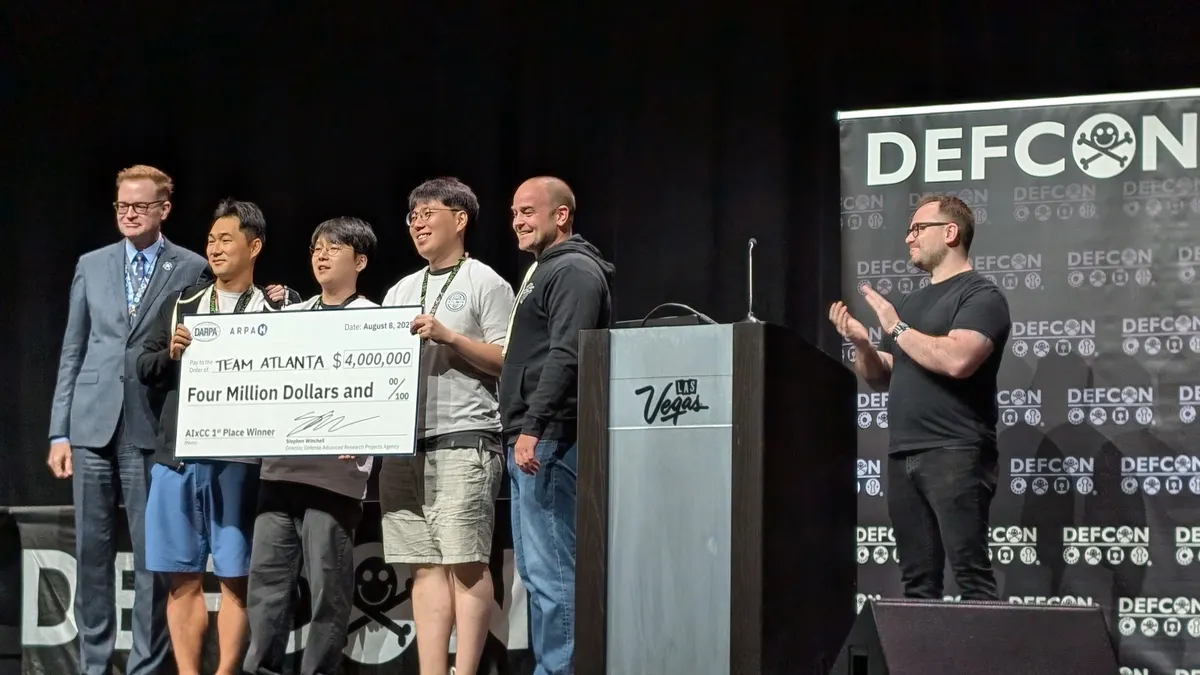
How a government contest launched a revolution in AI-based bug hunting
Security researchers have spent months honing AI systems that can find and fix serious vulnerabilities. Critical infrastructure everywhere could benefit.
By Eric Geller • May 18, 2026 -
MSPs need AI to fight AI-fueled cyberthreats: Guardz
Entry points haven’t changed, but the speed and scale of attacks have intensified, the security vendor found.
By Kelly Teal, Channel Dive contributor • May 15, 2026 -
More money is going to physical security, but it’s often CISOs that oversee it: EY
Organizations should centralize physical security and cybersecurity so both are adequately prepared for, the consulting firm says in a survey report.
By Robert Freedman • May 14, 2026 -
Frontier AI models reap rapid discovery of security vulnerabilities
Security teams have just a few months before AI-driven exploitation becomes the norm, researchers warn.
By David Jones • May 14, 2026 -
OpenAI launches Daybreak to combat cyber threats
The cybersecurity initiative uses AI to detect software vulnerabilities, partnering with Cloudflare, Cisco and CrowdStrike to counter threats.
By Paige Gross • May 13, 2026 -
Sponsored by Guardrail Technologies
Guardrail Technologies launches Traffic Light for Code & AI™; first security technology to verify & secure AI code and the people creating it
PARK CITY, Utah (May 5, 2026) — Guardrail Technologies, the leading provider of AI security and governance software for enterprises building with AI, today announced the launch of Traffic Light for Code & AI™, which verifies both the code AI generates and the people...
May 12, 2026 -
Identity takes center stage as a leading factor in enterprise cyberattacks
A new report shows two-thirds of ransomware attacks began with an identity-related breach.
By David Jones • May 12, 2026 -
AI and an absent government: Takeaways from RSAC 2026
Cybersecurity professionals discussed the balance between autonomy and oversight at the recent conference.
By Eric Geller • May 12, 2026 -
Deep Dive
New cybersecurity industry coalition aims to lead US critical infrastructure protection
The new Alliance for Critical Infrastructure’s biggest goal: changing how the nation plans for a major cybersecurity crisis.
By Eric Geller • May 11, 2026 -
Anthropic’s Claude used in attempted compromise of Mexican water utility
Researchers warn the incident highlights how AI tools can help untrained threat actors develop complex cyberattack capabilities.
By David Jones • May 8, 2026 -
Businesses eager but unprepared for AI to transform their security strategies
Meanwhile, a new report found, companies are neglecting other basic security tools.
By Eric Geller • May 6, 2026 -

 R. Eskalis/NIST. Retrieved from NIST.
R. Eskalis/NIST. Retrieved from NIST.
NIST will test three major tech firms’ frontier AI models for cybersecurity risks
After Anthropic’s announcement of Claude Mythos, agencies across the government are racing to get ahead of new AI models’ potential dangers.
By Eric Geller • Updated May 21, 2026 -
CISA urges critical infrastructure firms to ‘fortify’ before it’s too late
As concerns mount about potential cyber sabotage by the Chinese government, the U.S. is warning operators to practice maintaining services in a degraded state.
By Eric Geller • Updated May 5, 2026 -
White House questions tech industry on defensive AI use, cybersecurity resilience
Companies may be reluctant to answer some of the government’s questions, given the sensitive topics they address.
By Eric Geller • May 1, 2026 -
US and allies urge ‘careful adoption’ of AI agents
New guidance from a coalition of Western governments underscores the difficult-to-predict risks of still-evolving agentic tools.
By Eric Geller • May 1, 2026 -
PwC partners with Google Cloud to take on the managed security market
The professional services firm is stepping up its managed security ambitions with a Google Cloud-powered service that leans on agentic AI. The target market is companies that have outgrown DIY security.
By Nidhi Sharma • April 30, 2026 -
US agencies promote zero-trust practices for operational technology networks
Many zero-trust defenses work differently in industrial environments than in traditional business networks, five federal agencies said in newly published guidance.
By Eric Geller • April 30, 2026 -
State CISOs losing confidence in ability to manage cyber risks
Deloitte-NASCIO study shows AI, budget pressures are forcing states to make tough decisions.
By David Jones • April 29, 2026 -
Sponsored by Lenovo
When security becomes the attack surface: Why endpoint protection must evolve
When attackers target security tools, protection must be resilient, self-healing and always on.
By Nima Baiati, Vice President and General Manager, Commercial Software & Security Solutions, Lenovo • April 27, 2026 -
Hasbro expects March cyberattack to impact second-quarter revenue
The toymaker is reviewing files and working to fully bring certain systems back online. The company will incur some costs related to the investigation.
By David Jones • April 24, 2026 -
AI-written software creates hassles for wary security teams
A new report explains what cybersecurity practitioners need to see before they trust AI coding tools.
By Eric Geller • April 23, 2026