Cyberattacks: Page 3
-
Stryker’s manufacturing, shipping disrupted after cyberattack
The medtech company says it's still experiencing issues with order processing, manufacturing and shipping.
By Ricky Zipp , David Jones • March 13, 2026 -
Even primitive AI-coded malware helps hackers move faster, thwart attribution
IBM researchers discovered an autonomously coded backdoor that they called unsophisticated but nonetheless ominous.
By Eric Geller • March 13, 2026 -
 Explore the Trendline➔
Explore the Trendline➔
 Getty Images
Getty Images
-
5 ways to protect manufacturing companies from cyberattacks
Manufacturing suffered the most cyberattacks of any industry last year. Experts have advice about hardening networks and avoiding common mistakes.
By Jeffrey Kinney • March 12, 2026 -
Stryker investigating cyberattack that caused widespread outage
The full scope of the impact on the medical equipment firm, including operational and financial effects, remains unclear.
By Ricky Zipp , David Jones • Updated March 12, 2026 -
State-linked actors targeted US networks in lead-up to Iran war
Researchers found backdoors installed on U.S. company networks in the weeks prior to the U.S. and Israeli bombing campaign.
By David Jones • March 9, 2026 -
Ransomware is now less about malware and more about impersonation
Stolen passwords have replaced infectious code as the most common tactic in major breaches, Cloudflare said.
By Eric Geller • March 3, 2026 -
University of Mississippi Medical Center reopens clinics after ransomware attack
The academic medical center’s clinics can once again access patient records and are resuming normal operations more than a week after the attack.
By Emily Olsen • Updated March 2, 2026 -
UFP Technologies investigating cyberattack that impacted company data
The medical device maker warned of short-term shipment delays, but does not see a material impact.
By David Jones • Feb. 26, 2026 -
AI accelerates lateral movement in cyberattacks
New research paints a grim picture of how the technology is making cyberattacks faster and easier for threat actors.
By Eric Geller • Feb. 26, 2026 -
CISA orders agencies to patch Cisco devices now under attack
The vulnerabilities, scored as critical, affect the company’s software-defined wide-area networking (SD-WAN) systems.
By Eric Geller • Feb. 25, 2026 -
China-linked hackers breached dozens of telecoms, government agencies
The cyberattacks used a clever technique: malware that hid in plain sight on Google Sheets.
By Eric Geller • Feb. 25, 2026 -
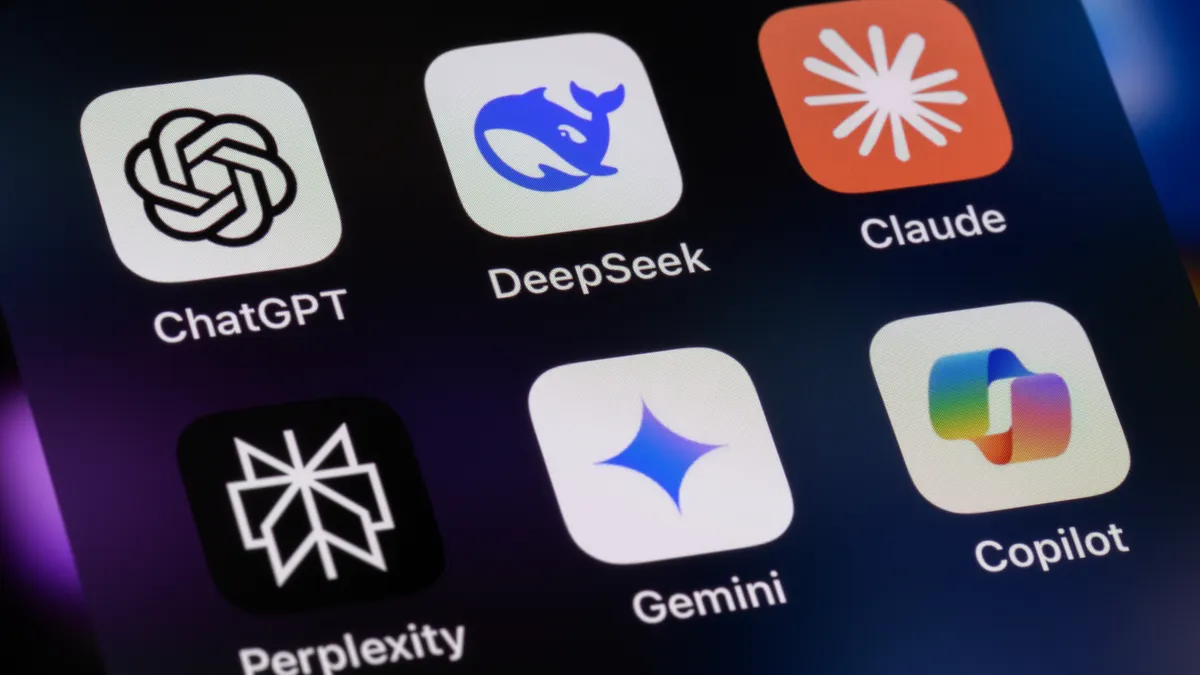
In the AI era, CISOs worry about data leaks and doubt tech will solve skills gaps
CISOs see AI as necessary but insufficient technology and fraught with risks, a new report found.
By Eric Geller • Feb. 24, 2026 -
AI helps novice threat actor compromise FortiGate devices in dozens of countries
Generative AI tools analyzed target networks and wrote exploit code, enabling an opportunistic attacker to have an outsized impact, according to a new Amazon report.
By Eric Geller • Feb. 23, 2026 -
Identity and supply chain need more attention, risk intelligence firm says
Roughly a third of attacks now use stolen credentials, according to the company’s latest report.
By Eric Geller • Feb. 18, 2026 -
Threat groups use AI to speed up and scale cyberattacks
A report from Palo Alto Networks finds hackers are increasingly using stolen identities and exploiting critical vulnerabilities within minutes of disclosure.
By David Jones • Feb. 18, 2026 -
Data-only extortion grows as ransomware gangs seek better profits
Businesses should prioritize securing one type of technology in particular, the security firm Arctic Wolf said in a new report.
By Eric Geller • Feb. 17, 2026 -
Ransomware attacks increase against IT and food sectors
Social engineering and zero-day vulnerability weaponization are getting faster and easier, two information sharing and analysis centers said in new reports.
By Eric Geller • Feb. 13, 2026 -
SmarterMail facing widespread attacks targeting critical flaws
The business email and collaboration software is being exploited for potential ransomware.
By David Jones • Feb. 12, 2026 -
Extortion attacks on the rise as hackers prioritize supply-chain weaknesses
Consulting firms and manufacturing companies accounted for many of the ransomware victims posted to the dark web in 2025, Intel 471 said.
By Eric Geller • Feb. 11, 2026 -
Polish power grid hack offers lessons for critical infrastructure operators, CISA says
The agency listed several steps businesses could take to prevent similar cyberattacks.
By Eric Geller • Feb. 10, 2026 -
Ransomware attacks against education sector slow worldwide
The U.S. saw the highest number of education-related ransomware attacks in 2025, at 130, despite a 9% decline year over year.
By Anna Merod • Feb. 6, 2026 -
Asian government’s espionage campaign breached critical infrastructure in 37 countries
The victims included national telecommunications firms, finance ministries and police agencies, with most targets suggesting an economic focus, Palo Alto Networks said.
By Eric Geller • Feb. 5, 2026 -
Autonomous attacks ushered cybercrime into AI era in 2025
Malwarebytes urged companies to adopt continuous monitoring and lock down identity systems as AI models get better at orchestrating intrusions.
By Eric Geller • Feb. 4, 2026 -
AI-ISAC inches forward under Trump administration
The U.S. government is exploring different options for how the information-sharing organization should work, an official said.
By Eric Geller • Feb. 3, 2026 -
FCC urges telecoms to boost cybersecurity amid growing ransomware threat
The commission said it was aware of ransomware disruptions at a growing number of small and medium-sized telecoms.
By Eric Geller • Feb. 2, 2026