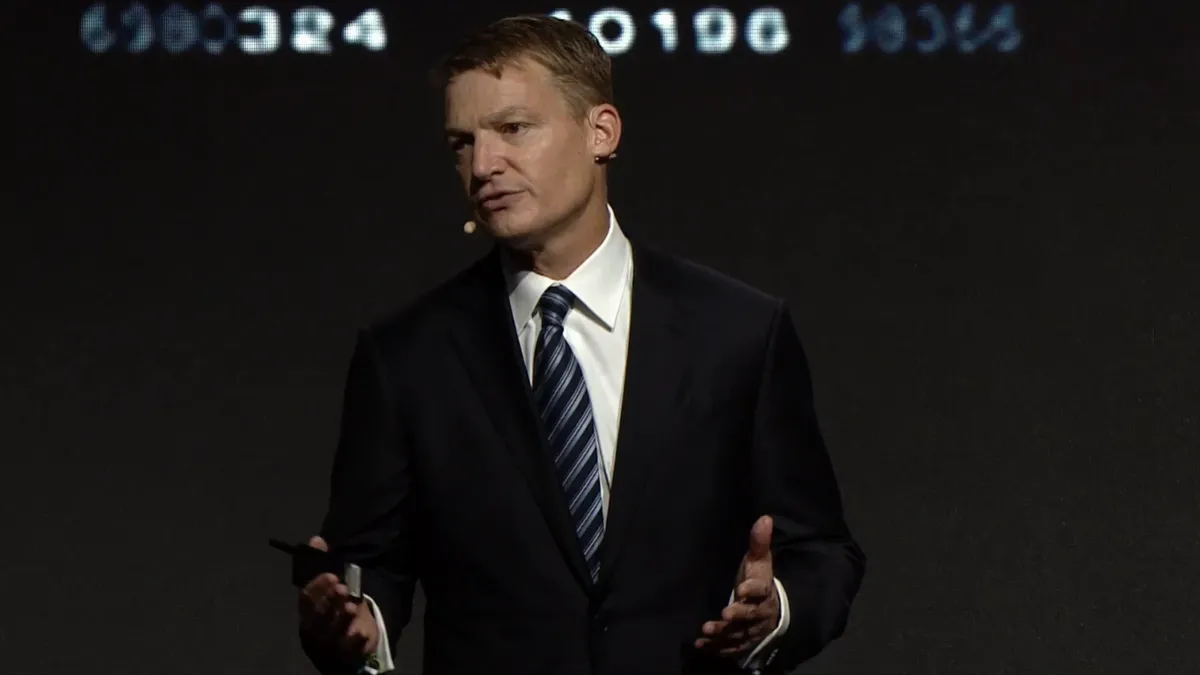
"2020 was a tough year to be a CISO," Mandiant CEO Kevin Mandia said during the Mandiant Defense Summit keynote Tuesday. "We have great people dealing with challenges they simply shouldn't have to address, but they have to."
In recent years, cybersecurity finally infiltrated overall business strategy until reaching a breaking point in 2020. A rapid descent into remote work in March 2020 pushed the CISO to the front of the C-suite; CISOs became operational.
CISOs "never had more influence than now — no exception," Mandia said. "There was a time in my career where CISOs almost advised IT … You're operational now, you have to make the things that are in your vision a reality."
Security executives becoming comfortable in a more operational role were met with unprecedented cyberattacks within the last year and a half: Ransomware pivoted from criminal gangs to nation-state actors. The private sector was dragged into attacks on federal agencies. And cyber policies were renewed purely out of reaction to a cyberattack.
For Mandia, the cybersecurity community took away lessons in at least three different threat categories: implants, zero days and ransomware.
When confronted with any of these threats, CISOs have to determine whether it's important to loop in their CEO. "And boy, is that a gut check," said Mandia. "You don't want to tell your board about an incident when it's pucker factor 10 out of 10. You want to tell them when its pucker factor is about three out of 10."
Given the last year of cyberthreats and attacks, security organizations are leaning more toward earlier involvement with their C-suite and board. CISOs may not have the full forensics or impact of an incident, but their boards are open to hearing about incidents early on.
"You have more control, take it while you can. Because if you don't, your remit will shrink by those who are capable of operating your security program," Mandia said.
Implants
SolarWinds became the poster child for implant threats, though it is far from the only case. Dating back to 2015, bad actors were drawn to attacking developers, including XcodeGhost, KeRanger, NotPetya and CCleaner, according to Palo Alto Networks' Unit 42.
Attacks using implant tactics can be "fair game for espionage," Mandia said, especially because international cyberespionage rules are a gray area. "The reason to do espionage is because there's asymmetry somewhere." If other nations cannot compete on land or in the air, they might find they can cultivate the best talent in cyber.
Implant attacks will also show up in the supply chain. The Biden administration has formally addressed supply chain security at least twice — in the May executive order and the August White House summit with CEOs from big tech. The White House wants to see tech companies make technologies that are easier to defend, but more difficult to attack, essentially.
FireEye "lived the process" of a supply chain compromise during the SolarWinds hack, said Mandia. It was one of, if not the first organization, to find and disclose the breach. The process includes questioning what vendors or partners the business relies on, and which of those suppliers are most significant to business continuity.
The SolarWinds implant attack proved the importance of information sharing. When a company confirms a breach internally, "you have no idea what the impact is immediately," Mandia said. While federal breach notification or incident disclosure laws are lingering in Congress, the issue companies might run into is that unknown impact factor. But "right now, to defend against implants, one of the most important things you got to do is let the world know about them as soon as you can," Mandia said.
Zero days
Static controls will not defend against implant or zero-day threats. Companies cannot rely on luck to create compensating controls when static controls didn't spot an anomaly first.
The number of known zero days in 2021 (64 zero days) is more than those found in 2019 (32 zero days) and 2020 (30 zero days) combined, Mandia said. Mandiant defines these zero days as attacks that were exploited in the wild.
The good news is, "it's getting harder to get in," said Mandia. The bad news? The market for zero days is growing. "It used to be that zero days were the prominence of nations; they developed them, or they bought them, and they used them. Now we're seeing far more criminal activity using zero day attacks," he said.
Remediation for zero days usually falls into basic cyber hygiene and patching.
Ransomware
Ransomware is "changing how we do business," Mandia said. Because of the escalating sophistication of ransomware, the early focus on email security and training is beginning to wane.
The coordination among ransomware gangs and their affiliates upped the ante on how damaging and targeted an attack can be. There are ransomware actors that "crafted ransomware that is so articulate in its capability that you can say, 'You know what? I don't want the key that decrypts everything … But can I decrypt this file?'" Mandia said. The ransomware actor can oblige, asking for a reduced payment in exchange for a smaller decryption key. "They can decrypt by file, by system, by campaign, by company. It's pretty elaborate."
There are two primary continuity considerations following a ransomware attack, including privileged access reduction and segmentation, and backups. Boards want to know how long it will take to resume operations when an attack occurs. This issue, however, isn't limited to ransomware.
"What happens if we lose the Miami office? Could be a hurricane or could be ransomware. It's really the same question," Mandia said.
Resilience is something CISOs will have to dry run, just like testing for how ransomware could access a system. For Mandia, preparation for a ransomware attack cannot necessarily be assessed in dashboards or technology purchases. Red teaming is the only way to uncover a business's "unvarnished truth," he said.
"Were we compromised? Yes or no? If so, what adjustments will we make?" After every red team attack, the security organization will refine its strategy and solutions, Mandia said.