UPDATE: June 8, 2022: A threat actor identified as TA570 has been exploiting the Follina vulnerability, identified as CVE-2022-30190, to deliver Qbot malware, according to Proofpoint researchers.
“When vulnerabilities are published, especially those with known proof of concepts and those that impact commonly used software and services, threat actors are quick to take advantage,” Sherrod DeGrippo, VP of threat research at Proofpoint.
UPDATE: June 6, 2022: Proofpoint researchers blocked a phishing campaign from a suspected state-aligned threat actor trying to exploit the "Follina" vulnerability, according to Twitter post Friday.
The campaign used an RTF and pretended to reference a salary increase. More than 1,000 messages were sent to fewer than 10 Proofpoint customers, including European and local U.S. governments, the company said in a statement.
“The extensive reconnaissance conducted by the second Powershell script demonstrates an actor interested in a large variety of software on a target’s computer,” Sherrod DeGrippo, VP of threat research and detection at Proofpoint, said.
Dive Brief:
- The Microsoft Office zero day vulnerability, dubbed "Follina," has the potential to spread significant impacts across the globe after security researchers identified threat activity in the wild. The timeline of the vulnerability has expanded and Microsoft has yet to issue a patch.
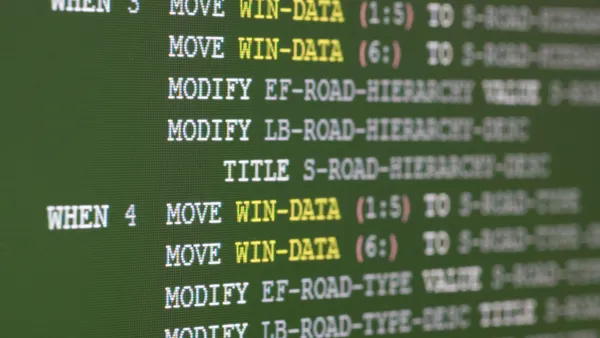
- Proofpoint researchers said an advanced persistent threat (APT) actor, identified as TA413, is using URLs to deliver Zip archives with Word documents using the technique. The threat actor, linked to China, has in the past targeted dissidents linked to Tibet and European diplomatic and non-profit organizations.
- Researchers found and notified Microsoft about the vulnerability in April, but the company did not consider the issue a security problem, according to researcher Kevin Beaumont.
Dive Insight:
Security researchers say there is the potential for significant impact on businesses worldwide, as millions of enterprise users depend on Microsoft Office to conduct business. The company has thus far only issued workarounds for the vulnerability.
Microsoft warned late Monday the vulnerability, if successfully exploited could allow an attacker to install programs, change or delete data or create new accounts.
The most common method of delivering Follina would be through email campaigns that entice users to download attached files.
“At this point, most organizations in both the public and private sectors know the dangers of malicious attachments, but they still need to open them to do business – employees receive at least a few attachments each week,” said Johannes Ullrich, dean of research at SANS Technology Institute. “So this will make an already popular exploit vector a lot easier to execute. The damage could be significant and the impact is global.”
The vulnerability is so serious, Ullrich said, that users can potentially trigger the exploit by previewing the document in Windows Explorer, without the need for a full download.
Recorded exploits thus far have involved Microsoft Word or Outlook, but in theory any Office document that handles OLEObject relationships is vulnerable to Follina, according to Nikolas Cemerikic, cyber security engineer at Immersive Labs.
“As OLEObject relationships are not specific to Word, it is likely that in the future we may see this vulnerability being exploited in other Office applications as well,” Cemerikic said.