Iran-linked hackers’ targeting of critical infrastructure threatens more than 5,000 industrial control devices around the world, including roughly 3,900 in the U.S., new data shows.
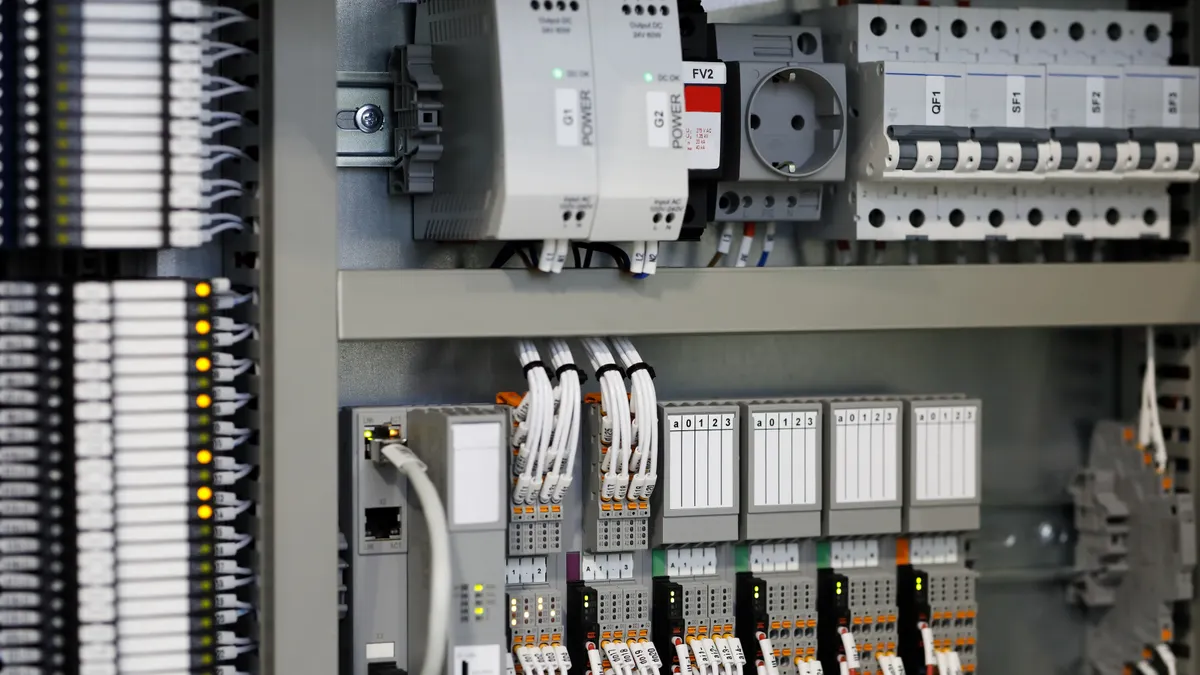
U.S. government agencies recently warned that hackers working on behalf of the Iranian regime were trying to compromise infrastructure operators by breaking into their Rockwell Automation-made Allen-Bradley programmable logic controllers (PLCs), and the U.S. has the most such devices of any country, according to a new report from internet monitoring firm Censys.
“Geographic distribution is heavily skewed toward the United States, which accounts for 74.6% of global exposure,” Censys researchers wrote, “consistent with Rockwell’s dominant market position in North American industrial automation.”
PLCs are industrial computers that control factory equipment, energy distribution technology and other infrastructure machinery. Iran-affiliated groups previously used weaknesses in these PLCs to breach infrastructure operators in 2023, and they recently resumed that activity in response to the U.S. and Israeli war.
The vast majority of the internet-connected PLCs Censys found were networked through cellular modems, suggesting their deployment in remote areas as part of geographically dispersed — and now technologically vulnerable — infrastructure networks.
“These devices are almost certainly field-deployed in physical infrastructure (pump stations, substations, municipal facilities) with cellular modems as their sole internet path,” Censys said.
Some devices are connected through Starlink satellite terminals, which Censys said made them even more “difficult to monitor and patch.”
PLCs exposed in many ways
While Censys initially scanned for PLCs responding over a common industrial equipment networking protocol, the company said many of the devices it detected were also accessible through other, more common services, such as HTTP, VNC and FTP.
“These services expand the available attack surface,” Censys warned, “and in several cases represent direct paths to operational impact independent of PLC exploitation.”
VNC access between the PLCs and their controlling computers is particularly alarming, Censys said, because the U.S. government advisory about Iran-linked hacking activity mentioned exactly that pathway for manipulating industrial control systems.
Nearly 300 devices are accessible through the unencrypted Telnet protocol, which Censys said had “no place on internet-facing [operational technology] infrastructure.”
Advice to infrastructure operators
Censys urged any company or public utility using Allen-Bradley PLCs to: immediately disconnect those PLCs from the public internet by routing traffic through secure gateways; log inbound traffic from ports and IP addresses associated with the Iran-linked hackers; and implement multifactor authentication for remote access to OT devices.
In addition, the company said, operators should disable or apply firewalls to VNC, Telnet and FTP services and replace PLCs with limited update support.